Evasion is a cat and mouse game in the cybersecurity field. Lets dive deep into it and see some simple tricks for deception.
Process ID (PID) spoofing is a sneaky technique used by malware to trick computer systems. Every program running on a computer is given a unique identification number called a Process ID, or PID for short. This PID helps the system monitoring each program on a system level.
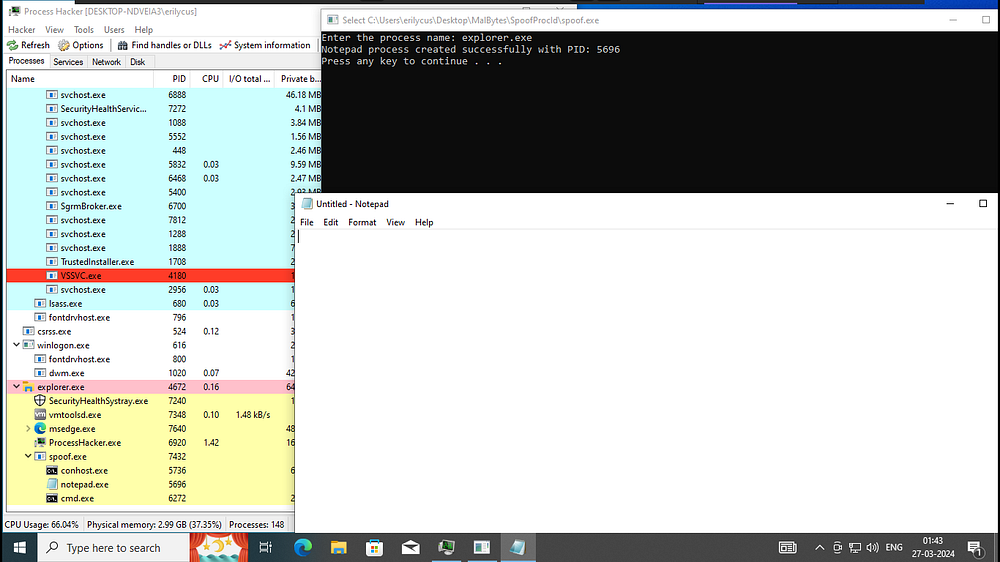
Now, imagine a scenario where a malicious program wants to hide its true identity and want to perform its malicious intents as a process created by a legit program on the system.
Example of svchost.exe with PID 860
PID spoofing is like putting on a disguise for that program. Instead of using its real PID, the program tricks the computer into giving it a different PID — one that looks innocent or belongs to a trusted program.
Why would a program want to do this ? Well, these might be some reasons —
1. Evade Detection: Picture a sneaky intruder trying to blend into a crowd to avoid being noticed. Similarly, a malicious program, by changing its PID, can slip past security software like a chameleon hiding in plain sight. This lets it fly under the radar, avoiding any alarms or alerts that might give away its presence.
2. Bypass Access Controls: Think of PID spoofing as forging a VIP pass to gain access to restricted areas. By pretending to be another process with a legitimate PID, a malicious program can trick the system’s access controls and sneak into places it shouldn’t be allowed.
3. Hide its Activities: PID spoofing lets a malicious program disguise its actions, making it harder for system administrators and security analysts to spot any suspicious behaviour. By acting like just another innocent process, it can carry out its nefarious deeds without raising any red flags.
4. Maintain Persistence: Malicious programs often aim to maintain persistence on a compromised system to ensure long-term access and control. By posing as a legitimate process, a malicious program can embed itself deeply within the system, making it much harder to root out and remove.
5. Facilitate Multi-Stage Attacks: In sophisticated cyber attacks, multiple stages are often involved, each carried out by different components or programs. PID spoofing helps cloak the activities of these components, making it a real challenge for defenders to trace the attack back to its source.
How does it work?
Trickery and deception are the main pillars of modern hacking !!! Malicious programs use clever tricks to fool the computer’s operating system or exploit weaknesses in its defences and carry out their intents.
Lets Explore:
#include <windows.h>
#include <iostream>
#include <tlhelp32.h>
#include <psapi.h>
#include <string>
// Getting Process With Its Name
DWORD GetProcessIdByName(const wchar_t* processName) {
PROCESSENTRY32W pe32;
HANDLE hSnapshot;
DWORD pid = 0;
// Taking a Snapshot of Proceess on Memory at Runtime
hSnapshot = CreateToolhelp32Snapshot(TH32CS_SNAPPROCESS, 0);
if (hSnapshot == INVALID_HANDLE_VALUE) {
std::cerr << “Error: CreateToolhelp32Snapshot failed (“ << GetLastError() << “)\n”;
return 0;
}
pe32.dwSize = sizeof(PROCESSENTRY32W);
if (Process32FirstW(hSnapshot, &pe32)) {
do { // Itertaing Through Each Process To Find The Required One
if (wcscmp(pe32.szExeFile, processName) == 0) { // Mathing ExeFile Name With Process Name
pid = pe32.th32ProcessID; // Retriving Its PID
break;
}
} while (Process32NextW(hSnapshot, &pe32));
}
CloseHandle(hSnapshot);
return pid;
}
int main(void) {
std::wcout << L”Enter the process name: “; // Geting Process Name
std::wstring targetProcessName;
std::getline(std::wcin, targetProcessName);
DWORD targetProcessId = GetProcessIdByName(targetProcessName.c_str());
if (targetProcessId == 0) {
std::cerr << “Error: Process ‘” << &targetProcessName << “‘ not found\n”;
return 1;
}
PROCESS_INFORMATION pi;
STARTUPINFOW si = { sizeof(si) };
si.cb = sizeof(STARTUPINFOW);
si.dwFlags = STARTF_USESTDHANDLES; // Indicate the use of standard handles
si.hStdInput = GetStdHandle(STD_INPUT_HANDLE);
si.hStdOutput = GetStdHandle(STD_OUTPUT_HANDLE);
si.hStdError = GetStdHandle(STD_ERROR_HANDLE);
// Specify the full path to the Notepad executable
std::wstring notepadPath = L”C:\\Windows\\System32\\notepad.exe”;
// Create a new process (Notepad) with the specified parent process
if (!CreateProcessW(nullptr, const_cast<LPWSTR>(notepadPath.c_str()), nullptr, nullptr, FALSE, 0, nullptr, nullptr, &si, &pi)) {
std::cerr << “Error: CreateProcess failed (“ << GetLastError() << “)\n”;
return 1;
}
std::wcout << L”Notepad process created successfully with PID: “ << pi.dwProcessId << std::endl;
system(“pause”); // Holding Console Window
CloseHandle(pi.hProcess);
CloseHandle(pi.hThread);
return 0;
}
Lets Dive In :
Let’s break down the key aspects of the code and explain the theory behind them, referencing Microsoft Developer Network (MSDN) wherever applicable.
1. Getting Process ID by Name:
- The function
GetProcessIdByNamesearches for a process by its name using the Windows Tool Help Functions (CreateToolhelp32Snapshot,Process32FirstW,Process32NextW). - It takes a wide-character string representing the process name and returns the process ID (PID) if found.
2. Creating a New Process:
- The
mainfunction demands a process name . - It then calls
GetProcessIdByName()to obtain the PID of the specified process. CreateProcessW()is used to create a new process of the supplied program to retrive its PID.- _
STARTUPINFOWstructure (si) is initialised withsizeof(STARTUPINFOW)and flags indicating the use of standard handles. This is the main structure holding the PID of the supplied process . CreateProcessW()launches the specified process (notepad.exein this case) using the parameters provided.- If successful, it returns a nonzero value and populates the _
PROCESS_INFORMATIONstructure (pi) with information about the newly created process .
3. Standard Handles:
- Standard handles (
hStdInput,hStdOutput,hStdError) are used to specify the input, output, and error streams for the new process. - They are set in the
STARTUPINFOWstructure passed toCreateProcessW. - By default, these handles are set to the current process’s standard handles.
4. Inheritance of Handles:
- In this code, the
bInheritHandlesparameter ofCreateProcessW()is set toFALSE. - This indicates that the new process should not inherit the handles of the current process, ensuring that it doesn’t use the same error and output streams.
5. Error Handling:
- Error handling is implemented using standard error output (
std::cerr) and Windows error functions (GetLastError). - Error codes returned by Windows API functions are used to provide diagnostic information about the failure.
Why PID Spoofing is a problem?
Imagine your computer system is like a bustling city with different programs representing various citizens going about their daily activities. Each program has its own unique identification number called a Process ID (PID), which helps the system keep track of who’s who.
Now, think of PID spoofing as a sneaky impostor trying to get into the citywith an ID of some VIP already living inside.
This impostor can cause all sorts of trouble. It can sneak past security guards, access restricted areas, and carry out shady activities without anyone suspecting a thing. It blends in so well that it’s nearly impossible to tell the difference between.
For security experts, PID spoofing is a real headache. It’s like trying to catch a pickpocket in a crowded market — the disguise makes it incredibly challenging to spot the troublemaker among the innocent bystanders.
To tackle this problem, we need to stay vigilant, keep our defences strong, and be on the lookout for any suspicious behaviour. Cyberviemight help in this scenario. We are a team of experienced professionals. For More Info contact info@cybervie.com
Credits : @erilycus







