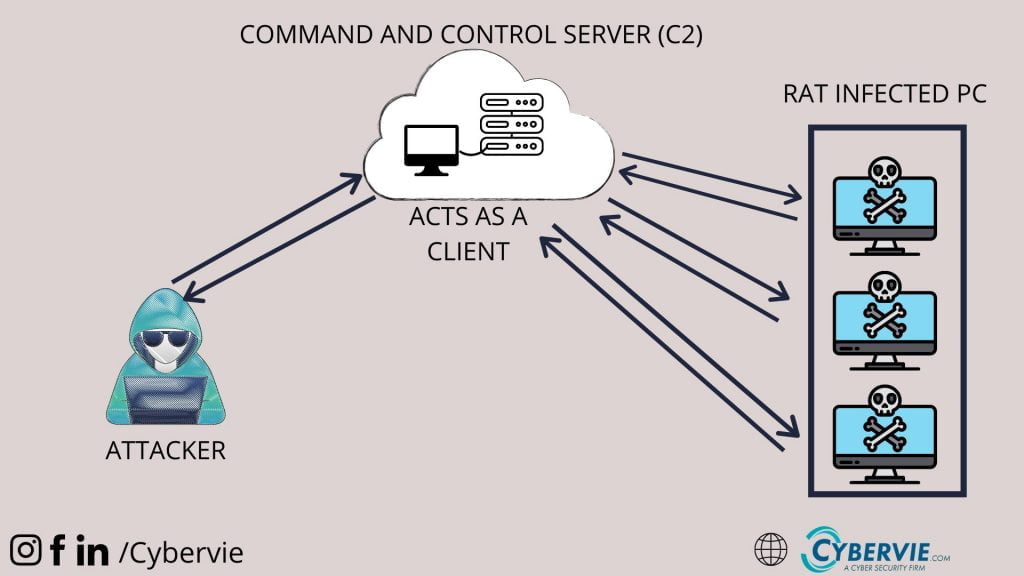
A Remote Access Trojan (RAT) is a malware that allows covert surveillance and unauthorized access to a victim’s machine.
These types of malwares are dangerous because they can give remote control over the compromised machine. The behavior of the Remote Access Trojan are similar in some ways to a keylogger, RAT also can record Keystrokes, usernames, passwords, screenshots.
But RAT’s can do more things than a keylogger, they can easily get your browser history, emails, and not only this but they can give total control over the compromised computer. That means you can read files, Change files, Open webcam, and they can even completely crash or brick your computer.
How the RAT can be installed in your computer?
They can be installed like any other malware.
Let’s see some of the techniques that can be used to install the RAT to your computer.
- Hacker can send some specially crafted email attachment which contains RAT.
- You can be tricked into download some malicious software or packages.
- It can be in a torrent file.
- Some of the specially crafted web-links can also directly download RAT to your Computer
RAT can be delivered to the victim with a social engineering or a physical access to the victim’s machines.
Some Common RAT’s
There are a large number of Remote access Trojan available on the internet to use.
Some of them are,
- SubSeven
- Back Orifice
- ProRat
- Turkojan
- Poison-Ivy
- XtremeRAT
- njRAT
And there lot more, a full list would be quite extensive and would continually growing
The dangerous part is that you can find and download these RAT’s from Google if you do enough searching. Although it’s recommended not to use RAT’s without permission or to harm anyone.
How to detect RAT?
The Detection of Remote Access Trojan can be difficult if it is specially crafted. Because the RAT does not shows up in the task manager’s currently running tasks. And It does not affect the speed of the system so you can’t tell if there is a change in a system after installing the RAT. To Detect these RAT you can use good and paid antiviruses and you can use malware detection tools.
If the RAT stays too long in your computer it can cause lots of damage and can collect lots of personal data.
How to be safe?
- Don’t download any software from untrusted websites.
- Never open email attachments from people you don’t know.
- Always keep your antivirus and system up-to-date.
- Don’t download torrent files from an unreliable sources.
- Always use reliable and reputed antivirus or anti-malware solutions.
- Be aware.







