Kali Linux 2021.2 just released with many changes and enhancements and is ready to be downloaded(from Kali updated page). or Update if you have already installed it.
Quick Changelog Summary
- Releasing Kaboxer v1.0
- Releasing Kali-Tweaks v1.0 – Easier to configure Kali Linux to your taste
- Refreshed Bleeding-Edge branch – An entire makeover for our backend that produces packages for the newest updates
- Disabled privileged ports – Opening a listener on ports 1024/TCP-UDP and below not requires root access
- New tools added – Ghidra & VS Code. alongside CloudBrute, Dirsearch, Feroxbuster, pacu, peirates, & Quark-Engine
- Theme enhancements – Added how to quickly swap between double & one-line terminal prompt and made Xfce4 Quick launch + file manager tweaks
- Desktop wallpaper & login background updates – Default images have changed with more to settle on from
- Kali NetHunter support for Android 11 – Android 11 support and various other improvements for the NetHunter platform
- More Docker support – Supporting ARM64 & ARM v7.
- Parallels support – Kali is fully supported for Apple M1 users who have Parallels.
- Various bug fixes – Pkexec patched, Wireshark permissions, command-not-found issues, & more accessibility features are all resolved
Introducing Kaboxer v1.0
Kaboxer is a kali application boxer that was installed in previous versions of kali Linux but does not behave correctly.
Apps in containers, for packages (a way forward for applications that are hard to package properly). But rather than being stand-alone containers, they’re integrated into the quality Kali package management systems and may be installed/removed through standard apt commands.
For developers, this is often an excellent new tool within the arsenal. Users will, hopefully, not realize that they’re using it, only noticing that previously problematic tools now work correctly!
Releasing Kali-Tweaks v1.0
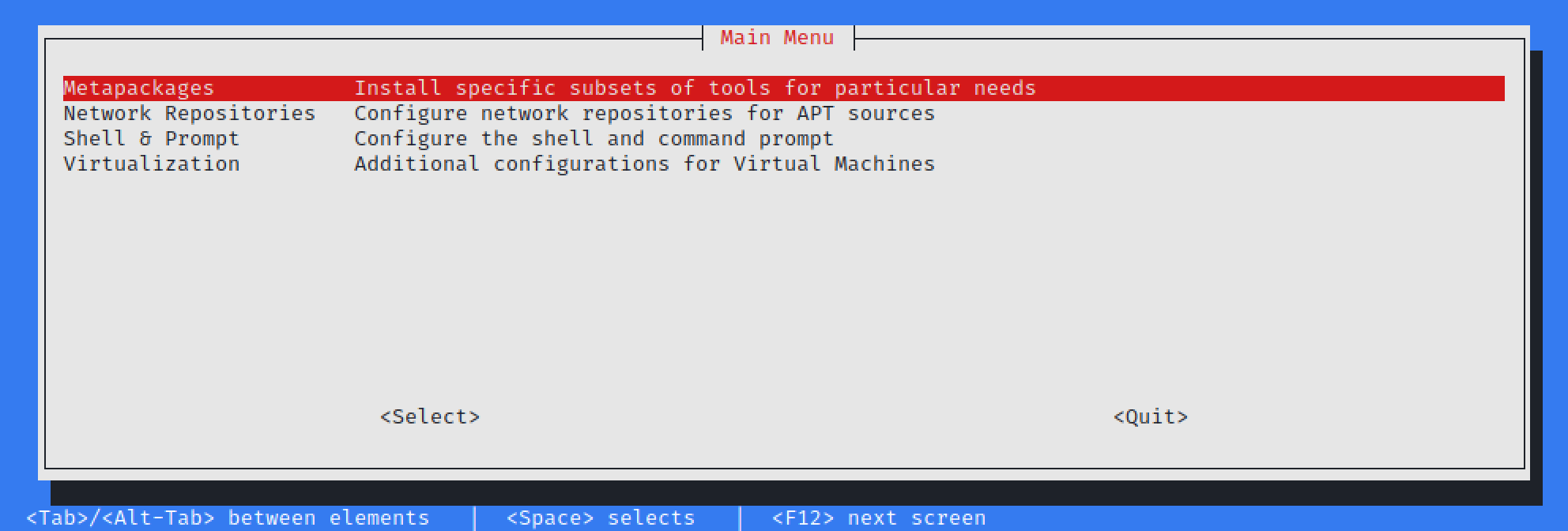
Kali-Tweaks! This package may be a little hand for Kali users, with the thought to assist customize Kali to your own personal taste quickly, simply, and therefore the correct way. this could assist you to prevent doing repetitive tasks.
Currently Kali-Tweaks will help with:
- Metapackages – Installing/removing groups of tools.
- Network Repositories – Enabling/disabling “bleeding-edge” branches.
- Shell & Prompt – Switch between two or one line prompt, enable/disable the additional line before the prompt, or configure Bash or ZSH as the default shell.
- Virtualization – Using Kali as a guest VM? Do a couple of actions to make the experience easier!
Refreshed Bleeding-Edge Branch
For those not too familiar with Bleeding-Edge branch, here is a breakdown:
- Kali by default opts to be stable where possible when packaging. This suggests some tools may appear “outdated”.
- We do this by looking to see when the tool author(s) signals “everything up to to this point is good”, by doing a “point release” (e.g.
1.0or2.1) - Developers often use source-code version control, allowing them to track any changes
- How programmers use source-code version control depends on their workflow, experience, and team size
- Developers can use a “tag” feature found in most source-code version control to signal when there is a new version (this is what Kali prefers)
- However, some people may say if it makes it to the “master” or “main” branch, then it is “production-ready”
- There are times where it has been “a while” (months or even years) since doing a tag for a stable release (aka point release), and people get frustrated that there are no updates (e.g. hashcat or impacket).
- In other cases, you would like the newest code which can include an exploit 0day (e.g. Metasploit-framework, Empire, or Exploit-DB) so waiting for a tagged release may not be an option
If you want to give it a try, have a look at our kali-bleeding-edge documentation to learn how to enable the repository and how to tell apt to select a package from this repository.
Disabled Privileged Ports
Patched the kernel to remove the restriction of requiring privilege permission in order to use TCP & UDP ports under 1024 (meaning 0/TCP-UDP <= 1023/TCP-UDP). This was done because:
- Kali is a desktop OS, rather than a server
- This “well-known” privileged port range is reserved for server services (e.g. 80/TCP HTTP, 443/TCP HTTPS)
- With the switch from Kali’s root to non-root user by default, rather than doing a port forward from outside the privilege ports to a restricted port, people were just running the program with super-user permissions instead
- It’s quicker to run: $ sudo <program>,
- Rather than remembering something like: $ sudo iptables -A PREROUTING -t nat -i eth0 -p tcp –dport 80 -j REDIRECT –to-port 8888
- This defeats the point of switching to a non-root user!
New Tools in Kali
Kali always add some new tools in it’s every release. Let’s see what has been added this time.
- CloudBrute – Find a company infrastructure, files, and apps on the top cloud providers
- Dirsearch – Brute force directories and files in web servers
- Feroxbuster – Simple, fast, recursive content discovery
- Ghidra – Reverse engineering framework
- Pacu – AWS exploitation framework
- Peirates – Kubernetes penetration
- Quark-Engine – Android malware scoring system
- VSCode a.k.a. Visual Studio Code Open Source (“Code-OSS”) – Code editor
Theme Enhancement Command Line
If you are using ZSH, with the latest Kali, you can toggle between the two-line prompt and one-line prompt by pressing: CTRL + p. This will only have an effect for the current session.
Kali NetHunter Updates
Plenty of improvements under the hood, including:
- Improved compatibility with dynamic partitions
- Improvements to the persistence of Magisk root
- Improvements to Bluetooth and settings menus
- Inclusion of
rtl88xxaupatches for older kernels within the kernel builder.
Now Kali Nethunter is available for
- Nokia 6.1
- OnePlus Nord
- OnePlus One
- Samsung Galaxy S20 FE 5G
- Xiaomi Mi A3
- Xiaomi Poco F1
Conclusion
These are all the new things in Kali 2021.2. We have seen some good patches of packages and new terminals Enhancements. Kali is also making a great progress in Nethunter. Hope they are going to develop Nethunter for more devices.
Check our blogs for more content like this







