In this article, we are going to discuss the most common printer hacking technique and also check why printers are vulnerable.
NOTE – For Educational Purpose Only
In the past few years, there has been a lot of mass printer hacking incidents. One of the best examples is when an attacker hacked around 50,000 printers all over the globe and print out the message to subscribe PewDiePie.

This was the message which get printed all over the globe from 50,000 printers.
Printer Hacking Vulnerability
The reason behind the massive 50,000 printer hack is just an open IPP port or port number 631.
Although there are few more ports that can led your printer exposed to internet like port 9100.
Internet Printing Protocol (IPP)
“The Internet Printing Protocol (IPP) is a specialized Internet protocol for communication between client devices (computers, mobile phones, tablets, etc.) and printers (or print servers). It allows clients to submit one or more print jobs to the printer or print server, and perform tasks such as querying the status of a printer, obtaining the status of print jobs, or canceling individual print jobs.” – Wikipedia
With the IPP port open, it is very easy to find approximately all the information about the printer such as printer name, location, model, firmware version, or even printer wifi SSID.
You can also send print jobs and even malicious files to printer if the IPP port is open.
According to surveys there are 80,000 vulnerable printers are opened in the world.
Now the thing is how to hack these printers.
Make sure you only use this method ethically to test the security of your own device.
How To Hack Printers
There are few ways to hack a printer.First let’s talk about how to hack printers near you and in your network.
we are going to use a tool name PRET
“PRET is a new tool for printer security testing developed in the scope of a Master’s Thesis at Ruhr University Bochum. It connects to a device via network or USB and exploits the features of a given printer language. Currently, PostScript, PJL, and PCL are supported which are spoken by most laser printers. This allows cool stuff like capturing or manipulating print jobs, accessing the printer’s file system and memory, or even causing physical damage to the device. All attacks are documented in detail in the Hacking Printers Wiki.” – Github
The main idea of PRET is to facilitate communication between the end-user and the printer. Thus, after entering a UNIX-like command, PRET translates it to PostScript, PJL, or PCL, sends it to the printer, evaluates the result, and translates it back to a user-friendly format. PRET offers a whole bunch of commands useful for printer attacks and fuzzing.

How to install PRET
You can install PRET by typing
git clone https://github.com/RUB-NDS/PRET && cd PRET
python2 -m pip install colorama pysnmP
(If you are using Kali linux 2021.2. you may have to install pip2 manually)
How to locate printers
You can run the program by typing
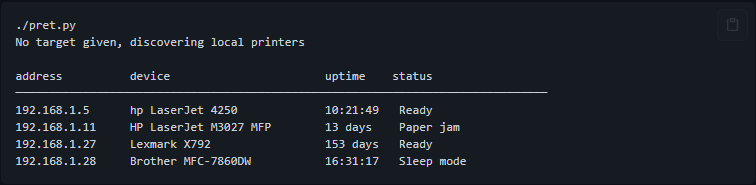
python pret.py or python2 pret.py or ./pret.py
This will locate all the printers near you and in your local network.
There are exactly three options you can try while exploiting the printer.
- ps (Postscript)
- pjl (Printer Job Language)
- pcl (Printer Command Language)
Not all languages are supported by printers. So you need to check different languages if you don’t get feedback from one language.
Now that you have discovered the printers near you it is time to exploit them.
There are 3 ways you can exploit them and with every way you can try all the tree languages to test.
python pret.py {IP} pjl
python pret.py laserjet.lan ps
python pret.py /dev/usb/lp0 pcl
Use last option if the printer is connected with you computer already.
If the command runs successfully you can be able to see a screen like below after typing help. It will show you all the different commands you can use.

PRET allows us to use all of these commands if the printer get connected successfully.
you can try this attack with you home printer yo see that if it is vulnerable or not.
Now, this the one way to attack the printer. but how attacker have exploited 50,000 printers all across the globe. so this is because IPP port and port 9100.
Using Shodan.io to Hack Printers
From shodan.io we can search for all the vulnerable device across the world. Shodan is a very powerful tool to find vulnerabilities, it can find vulnerable computers, cameras, printers almost everything which is connected to internet.
To search for vulnerable printers across the globe we have to type.
port:9100 pjl
This will search all the printer with open 9100 port which immediately accepted for printing.

Anyone can exploit all those open printers and create chaos. Shodan can not only find printers but every vulnerable thing which is connected to the internet. you have the IP address of the printers and you know they use pjl as a language. Now anyone can follow the above steps to hack all those printers and print anything.
In the case of 50,000 printers hacked the hacker used a bash script to automate the task. The script takes a list of printers with Shodan and cycles it to each PRET IP address with the commands specified in commands.
Anyway, if you want to test your printer’s vulnerability test it.
Printer Security Testing Cheatsheet – click here.
How to protect the printer?
All of these Printer hacking happens because most of people don’t know that their computer is up on internet. If not mandatory don’t connect you printer to internet and use it in your local network.
Other Precautions
- Disable printing over the internet
- Change your printer’s credentials if it uses one.
- Close the router’s ports 9100, 515, 721-731.
- Turn off the printer when not in use.
That’s it for today’s article. Find more interesting blogs on our blog page.









